 Here is why ALL computer users need to be vigilant. (Scroll down to read the 7 habits that can make your Internet surfing safer).
Here is why ALL computer users need to be vigilant. (Scroll down to read the 7 habits that can make your Internet surfing safer).
Today “one of the largest global cyber operations in history” attempted to take down the Blackshades racket. Here is why I think this is important news for you to know about.
Blackshades Malware sells to hackers for about $40. It has been available underground since 2010. Its street name is “W32.Shadesrat”. The word “rat” at the end of the name refers to Remote Access Tool. It infects Windows computers when people click on links (in email, or in your socials). Once on your machine, it silently captures usernames, passwords, instant messages, and FTP logins. This software can even fire up your computer’s video camera without you knowing it. How’s that for getting you all warm and fuzzy? (Note to computer makers: how about a sliding cover over our camera’s peepholes?)
Ok, so that’s what it does. Here’s the really disturbing part, in 2010 the code was leaked out to the Internet. Oops! In 2012 the developer was arrested. Booyah! In 2014, (CNN reports today) 18 countries including the US took part in a world-wide crack-down of some 300 hackers and 1,000+ storage devices in an effort to stomp Blackshades out. So, as is made clear by this timeline, removing the head does not a dead snake make.
The FBI site reports “the Blackshades RAT was purchased by thousands of people in more than 100 countries. Hundreds of thousands of computers are believed to have been infected.
So basically, there is this awesome software out there. It’s $40. Hackers love it. Presumably, its easy for anyone to use. It’s the backend of a hugely invasive, hard-to-detect pursuit of your data and your private information via electronic means. It’s not centralized. This software when leaked into the wild, took on a life of its own, and attacks have been growing ever since. The software can be deployed in a variety of schemes, which include getting Windows users to click on links that take them to the promise of seeing “images, videos or other items of interest.” Fabulous.
Hackers have been using off-the-shelf tools for a while. Some called “Script Kiddies” cobble together these little gems and send out their own bits of loveliness. What all this means to you is that you need to be ALERT when clicking on links or installing software. Sounds sort of crazy, hu? Just about everything that comes to you is in a link, like that raspberry-eating bunny video 11 million + of you have enjoyed.
Of course you need to be running virus protection on your computer. That’s a given. But you can’t solely rely on your virus software to catch everything, especially when stuff is being created and released practically on a daily basis. What you need to know are the 7 habits that can make your Internet surfing safer.
The 7 Habits of Securely Operating With the Internet
1. Install a virus program on your computer. Use Mac or Pc? I don’t care. Get virus protection. Install it. I like Intego for Mac. For the PC this has gotten a little more complex…er easier? With Microsoft Security Essentials (Defender) there was progress…but it seems that progress has slowed? Lately I’ve been recommending McAfee, Nod32 and Kaspersky. The problem with virus software in the past was that it slowed down your machine. Today, installing virus software on your machine can slow it down, depends on your processor. Test which application you like best. Make sure to keep your definitions up to date.
2. Demote your primary user account (the account you use the most) to just user, rather than Admin. Yes. This is a ROYAL pain in the ass. You never know how much you’re installing until you are stopped every time. Yes, this is probably the LEAST employed method of securing your machine. Yes, it’s one of the best ways to keep your machine from getting infected. Can’t install software, can’t get infected.
3. When installing ANY software on your PC, watch carefully for other elements that are automatically installed. I F-ing hate the way Adobe does this when you install their Acrobat Reader (pc only). It’s very easy to get your browser hijacked. The software supplants your search engine for it’s own crappy two bit piece of machine-slowing shit. Just fixed something like this for a friend by eradicating search.conduit.com from her computer. PS. developers of search.conduit.com you SUCK DONKEY BALLS. That’s right. You heard me.
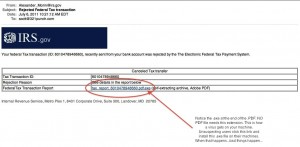
4. Never trust email from your bank or organization, or external links in your socials. (shortened Twitter links can be particularly insidious). Yes, sometimes your bank will email you, but MORE times than not a scammer will be trying to get you to click a nefarious link download their shit, or link you to their site so they can infect you. Better yet, they get you to enter your credentials into a fake command and control site. Entering your credentials into a fake site is called a Phishing Scam. VERY popular. See the Fig 1. image, its not exactly a phishing scam, but it certainly tried to get me to install a nefarious piece of software. Oh, and it was “from” the IRS.
5. Clone your machine. Offsite backups like Carbonite and Dropbox are great for handling your data. Really great. But if you suffer a major malfunction in your operating system, or your computer catches the equivalent of the clap, restoring from a clone is a whole lot faster than trying to download gigabytes of your stuff back down to your drive from some distant server.
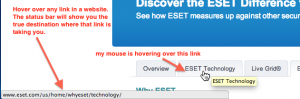
6. Mind your browser’s location and status bars when visiting anything. Ok. This might be a new one for you. There are two areas of your web browser that you need to pay attention to: a) the status bar b) the location bar. The status bar is in the lower left-hand corner of your browser. It appears when you hover over a link. See Fig. 2. If you don’t see the status bar appear when you hover over a link, be sure to turn ON the status bar (Google this for your particular browser).
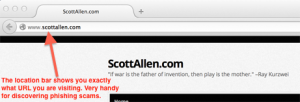
For the Location Bar, which is equally as important, you need to look at the very top of your web browser. This is where you type in website URLs, or where website URLs appear when you visit sites. See Fig. 3
7. Patch your system. We’ve all heard about the WinXp exploits. We’ve all heard about zero day exploits. The bottom line is this: when your system says it needs a patch (and the source of that message is verified as trusted) then by all means Patch that thing. Yes, sometimes patches result in user interface changes, which can really piss you off. But more often than not, what comes down in a patch is a fix for a recent exploit. Patches keep you safe. They also keep your machine running fast (usually). Ignoring patches exposes you (and your data) to bad guys. It’s as simple as that. I’d rather endure a little UI friction than catching a virus.
For further reading about Blackshades, here are the URLs I referenced for this article:
http://www.cnn.com/2014/05/19/justice/us-global-hacker-crackdown/index.html?hpt=hp_t1
http://www.bbc.com/news/uk-27471218
http://www.symantec.com/connect/blogs/blackshades-rat-usage-rise-despite-author-s-alleged-arrest
http://www.fbi.gov/newyork/press-releases/2014/remarks-prepared-for-delivery-by-special-agent-in-charge-leo-taddeo-at-blackshades-press-conference
http://thehackernews.com/2013/03/hacker-uses-evernote-account-as-command.html

